Learn more about the main email authentication protocols (SPF, DKIM, DMARC) and how they are used to verify email senders and improve deliverability.
Email authentication is a crucial line of defense against harmful email activity. This is especially important with the rise of email-based scams, such as email spoofing and phishing attacks. In fact, AAG estimates 3.4 billion phishing emails are sent each day.
For any email sender, authentication is also a key step to boost email deliverability. That’s because email authentication lets you prove to email providers like Gmail, Yahoo! Mail, and Microsoft Outlook that you’re authorized to send email messages.
This article will explain the three main email authentication methods — SPF, DKIM, and DMARC — and how to set them up for your sending domain.
What is email authentication?
Email authentication is the process of verifying your domain and email addresses before you can send email content through an email service provider (ESP).
There are three main email authentication methods: SPF, DKIM, and DMARC.
These authentication protocols help shield users and businesses from harmful email content. That’s because they deter scammers and prevent anyone from impersonating your organization.
Authenticated emails are also less likely to be marked as spam. This is key to maintaining your email sender reputation.
SPF, DKIM, and DMARC are complementary. It’s highly recommended to have one form of validation — and even better to use all three.Keep in mind that major mail servers now run stricter authentication checks for bulk senders.
In fact, Google now requires emails sent to Gmail accounts to have some form of authentication.
What is SPF?
SPF (Sender Policy Framework) is a security protocol that asks you to list which IP addresses can send an email from your domain. After an email is sent, the recipient’s server can check the SPF record in your Domain Name System (DNS). Through SPF lookup, they can verify whether the email is from an authorized sending server.

The SPF record that the server receives contains DNS TXT records. Each record is linked to a specific domain (or range of addresses/subdomains belonging to the same network). Here is an example of an SPF DNS TXT record with the authorized domain name:
Today, email senders without valid SPF records often go through rigorous authentication checks. And most of them end up in the spam folder.
Although SPF authentication can suffice sometimes, it doesn’t offer full protection from domain spoofing and other malicious email activity. You also need to update the records when you change Internet Service Providers (ISPs).
What is DKIM?
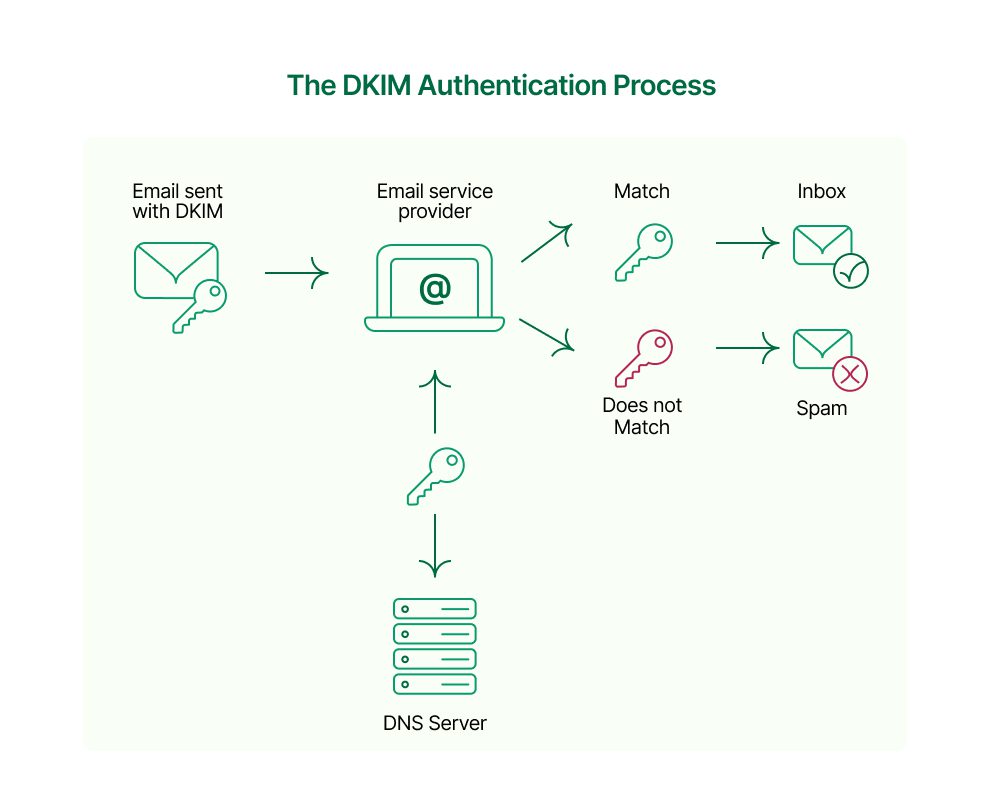
DKIM (DomainKeys Identified Mail) is another way to authenticate emails. Like SPF, DKIM uses DNS TXT records to verify the sender identity. One big difference is that DKIM uses cryptography instead of IP addresses.
DKIM relies on two encryption keys — one public and one private:
- The private key is accessible only to the domain’s owner. It creates a digital signature that you attach to your email header. This signature serves to authenticate your outgoing messages.
- The public key is accessible in the sender’s DNS server. Recipients use the public key to verify the DKIM signature in the message header.
Although DKIM authentication is more secure than SPF, they work better together to protect the email sender and receiver. Consider SPF and DKIM the ‘two-factor verification’ equivalent for email authentication.
What is DMARC?
DMARC (Domain-based Message Authentication, Reporting & Conformance) is a validation process that checks both SPF and DKIM records to verify emails. .
To create a DMARC record, you first need to have SPF and DKIM protocols in place. If the email passes both checks, it gets authenticated. If it doesn’t, you can set policy parameters to determine how the server should manage the email.
You will then receive DMARC reports explaining how the server handled emails that didn’t pass the authentication checks.
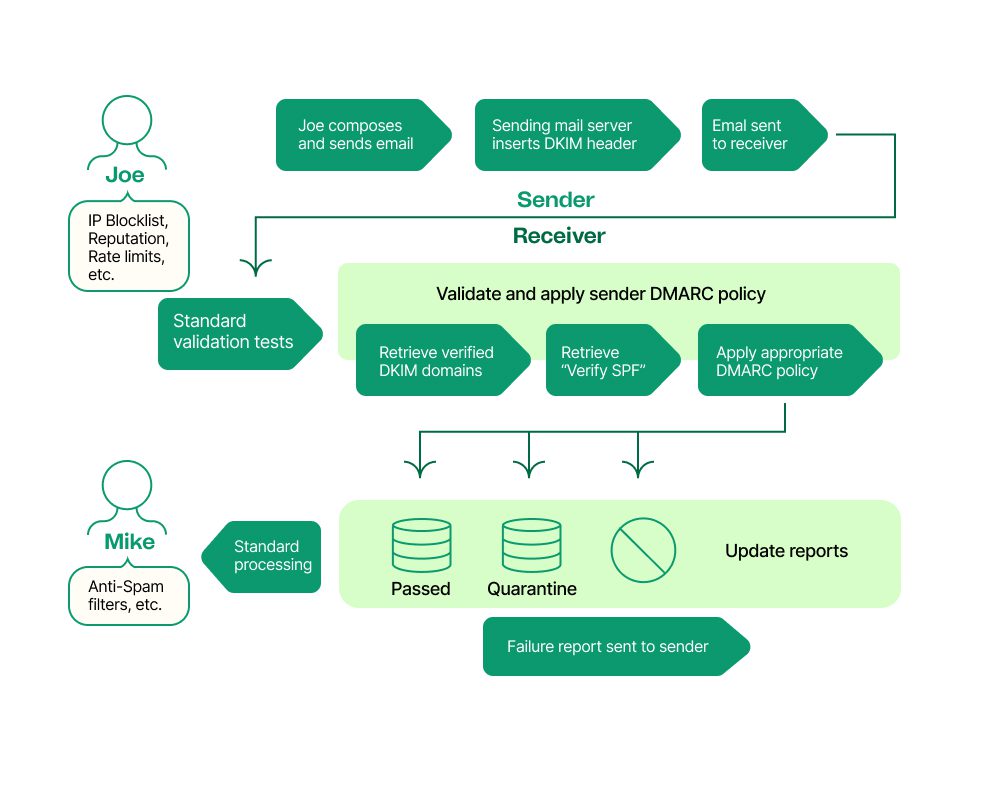
Here are a few examples of DMARC policies you can set as a domain owner:
- p=none — The receiving server does nothing
- p=reject — the receiving server rejects any mail that fails the authentication (SPF or DKIM)
- p=quarantine — the receiving server flags the unverified email for suspicious content and sends it to the spam folder
- v — the receiving server checks DMARC
Authenticate your domain to reach Gmail recipients
Beginning in February 2024, Gmail started requiring all bulk senders to follow stricter anti-spam guidelines. If you send more than 5,000 messages per day, you need to set up SPF and DKIM email authentication for your domain. This will prevent Gmail from blocking your messages or marking them as spam.
How does email authentication work in Brevo?
In addition to authenticating senders for your domain, you’ll also have to authenticate apps that send emails on your behalf. This includes email marketing platforms.
Luckily, Brevo makes it easy to authenticate your sending domain. Create your DNS record, set up DKIM, and get validation in minutes to keep reaching your Gmail and Yahoo subscribers.
Ready to get started? Brevo’s email API can send up to 120,000 emails per minute with the best possible delivery. Sign up today to send emails confidently and securely.






